THE NIST CYBER SECURITY FRAMEWORK
THE NIST CYBER SECURITY FRAMEWORK
General Overview
NIST is the National Institute of Standards and Technology at the U.S. Department of Commerce.
The NIST Cybersecurity Framework (CSF) is a set of guidelines developed by the National Institute of Standards and Technology (NIST) to help organizations manage and reduce cybersecurity risks, and protect their networks and data.1 Originally published in 2014 and updated in 2018, its most recent upgrades were to version 2.0 in February 2024.
The CSF was initially created for critical infrastructure sectors; but – although voluntary – has now been widely adopted across sectors globally. The NIST CSF gives your business an outline of best practices to help you decide where to focus your time and money for cybersecurity protection.
Evolution of the Framework
The original/ first version of the CSF was first released or published in the year 2014 by the Institute for
Standards and Technology in the United States. It has however, been upgraded twice after the first
version to reflect new changes and variations to the original version first published.
Thus, its evolution/trajectory can be broken down into three distinct versions:
- Version 1.0 – In 2014, the Initial release focused on critical infrastructure.
- Version 1.1 – In 2018, Provided Enhancements for supply chain risk and identity management.
- Version 2.0 – In 2024, expanded the scope to all organizations and added the “Govern” function.
Purpose
The entire purpose of the CSF could be summarized into:
- Provide a flexible, repeatable, and cost-effective approach to managing cybersecurity risk.
- Help organizations understand, communicate, and improve their cybersecurity posture.
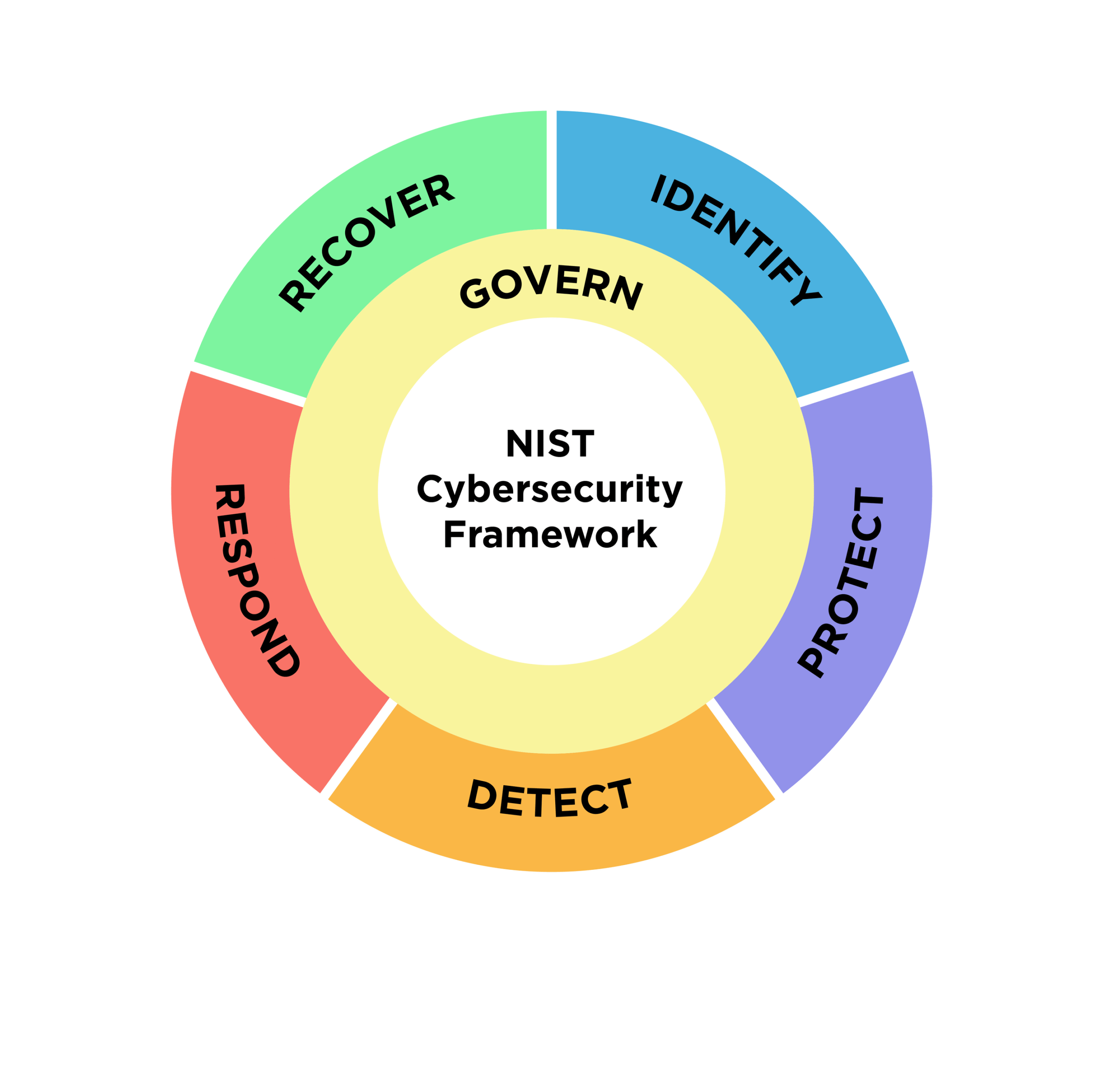
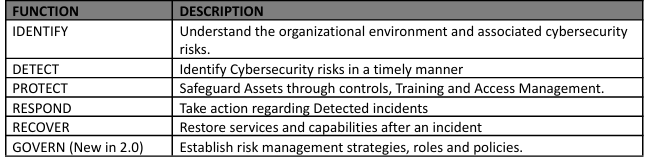
STRUCTURE / FUNCTIONS of the NIST CSF
The CSF is composed of three primary components: the Core, Implementation Tiers, and Profiles.
The Core outlines five key cybersecurity functions: Identify, Protect, Detect, Respond, and Recover, each
of which is further divided into specific categories and subcategories.
These functions offer a high-level,
outcome-driven approach to managing cybersecurity risks. In its most recent update in 2024, a new
function, “GOVERN” was introduced as its latest function.
The Implementation Tiers help organisations assess the sophistication of their cybersecurity practices, while the Profiles enable customisation based on an organisation’s unique risk profile and specific needs.
A - CORE
The CORE, being the crux and “Heart” of the entire Framework, provides the functions of the NIST
Cybersecurity Framework, and how it can be put to work in your business.
Its functions are seen in these
five areas: Identify, Protect, Detect, Respond, and Recover. A 6th function – “Govern” is included as one
of the functions in the most recent update to the CSF of 2024.
Some of the ways and manner in which
these functions can be carried out in various companies/workspaces include the following:
- Identify
- Make a list of all equipment, software, and data you use, including laptops, smartphones,
- tablets, and point-of-sale devices.
- Create and share a company cybersecurity policy that covers:
a. Roles and responsibilities for employees, vendors, and anyone else with access to sensitive data.
b. Steps to take to protect against an attack and limit the damage if one occurs.
- Protect
- Control who logs on to your network and uses your computers and other devices.
- Use security software to protect data.
- Encrypt sensitive data, at rest and in transit.
- Conduct regular backups of data.
- Update security software regularly, automating those updates if possible.
- Have formal policies for safely disposing of electronic files and old devices.
- Train everyone who uses your computers, devices, and network about cybersecurity. You can
- Help employees understand their risk in addition to their crucial role in the workplace.
- Detect
- Monitor your computers for unauthorized personnel access, devices (like USB drives), and software.
- Investigate any unusual activities on your network or by your staff.
- Check your network for unauthorized users or connections.
- Respond
Have a plan for:
- Notifying customers, employees, and others whose data may be at risk.
- Keeping business operations up and running.
- Reporting the attack to law enforcement and other authorities.
- Investigating and containing an attack.
- Updating your cybersecurity policy and plan with lessons learned.
- Preparing for inadvertent events (like weather emergencies) that may put data at risk.
- Test your plan regularly
- Recover
After an attack:
- Repair and restore the equipment and parts of your network that were affected.
- Keep employees and customers informed of your response and recovery activities.
- Govern
Thus, the CSF Core is the heart of the framework and includes six functions:
IMPLEMENTATION TIERS
They refer to the processes, customization and characterization of an organization’s cybersecurity risk governance and management practices put in place in the management of those risks. They could be described as how an organization views and handles cybersecurity risk, and might be categorized into the following:
- Tier 1 – Partial – Risk management is informal or ad hoc.
- Tier 2 – Risk Informed – Risk management practices are in place but not consistent.
- Tier 3 – Repeatable – Policies are formalized and regularly reviewed.
- Tier 4 – Adaptive – Cybersecurity practices are continuously improved and proactive.
PROFILES
A Profile represents the alignment of cybersecurity activities with business needs. A Profile enables organizations to establish a roadmap for reducing cybersecurity risk that is well aligned with organizational and sector goals, considers legal/regulatory requirements and industry best practices, and reflects risk management priorities, and also allows organizations to tailor the framework to their specific requirements and risk assessments.
Given the complexity of many organizations, they may choose to have multiple profiles, aligned with particular components and recognizing their individual needs. Framework Profiles can be used to describe the current state or the desired target state of specific cybersecurity activities.
The Current Profile indicates the cybersecurity outcomes that are currently being achieved. The Target Profile indicates the outcomes needed to achieve the desired cybersecurity risk management goals.
Organizations typically start by developing a “Current Profile” to describe their existing cybersecurity practices and outcomes. From there, they can create a “Target Profile” to outline the desired future state and define the steps needed to achieve it. Alternatively, organizations can adopt a baseline profile based on their sector or specific industry needs.
KEY FEATURES OF CSF 2.0
The NIST Cybersecurity Framework, considered to be a living document, states that it will be updated
and improved over time to keep up with changes in technology and cybersecurity threats, as well as to
integrate best practices and lessons learned.
Some of the major inclusions and updates made since the
inception and updated version 1.1 in 2018 include:
- Govern Function (New): Ensures executive accountability and alignment with enterprise risk.
- Expanded Scope: CSF 2.0 applies to organizations of any size, sector, or maturity.
- Improved Resources: Includes a CSF 2.0 Reference Tool and Quick Start Guides for small businesses and enterprises.
- Interoperability: Enhanced alignment with other frameworks like COBIT, ISO/IEC 27001, and NIST 800-53.
POSITIVES / ADVANTAGES
The Advantages / Benefits of adopting the NIST CSF into existing businesses cannot be overemphasized. Some of these include:
- It is customizable to your business context.
- It helps to improve risk management and cyber resilience.
- Enhances communication between technical and business stakeholders.
- Helps with compliance (e.g., HIPAA, FISMA, and GDPR).
- Facilitates continuous improvement and incident response planning.
Conclusion
The NIST Cybersecurity Framework offers a clear, flexible, and proven approach to managing cyber risks across any industry or organization size. Its six core functions viz; Identify, Protect, Detect, Respond, Recover, and Govern equip businesses with a structured roadmap for improving resilience, strengthening governance, and aligning cybersecurity with strategic goals. By adopting the CSF, organizations can not only defend against today’s threats but also build the adaptability needed to stay secure in a rapidly evolving digital landscape.
Recent Posts
- OVERVIEW OF WITHHOLDING TAX IN LIGHT OF THE2025 TAX REFORMS
- AN UPDATED OVERVIEW OF THE IMPACT OF THE PROPOSED WINDFALL TAX ON NIGERIA’S FINANCIAL SECTOR
- The Real Estate Conundrum in Nigeria
- THE LEGAL IMPLICATIONS OF DIGITAL LENDING IN NIGERIA:CONSUMER PROTECTION AND REGULATORY OVERSIGHT
- International Commercial Law (ICL): Trade Digitization

